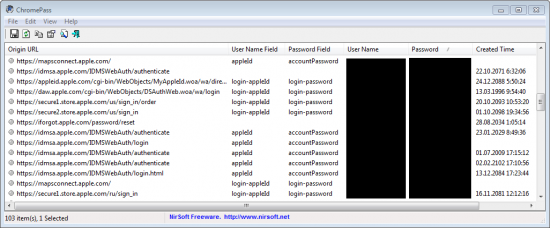
Acquiring and Utilizing Apple ID Passwords, Mitigating the Risks and Protecting Personal Information | ElcomSoft blog
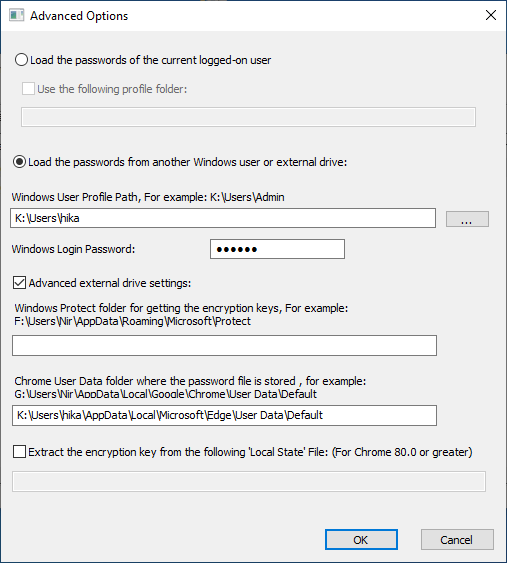
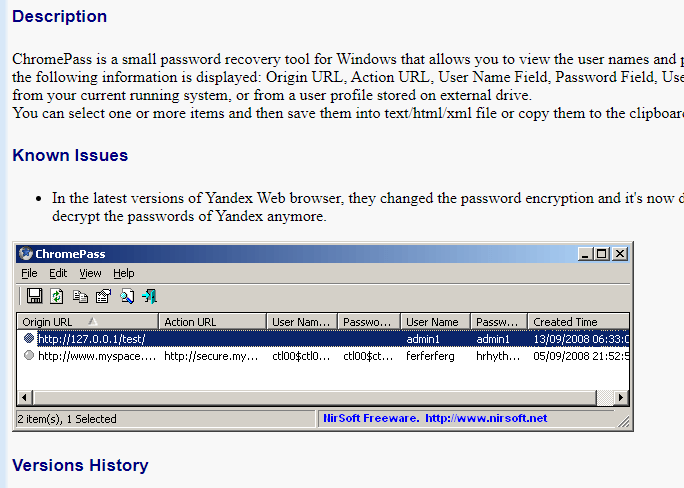
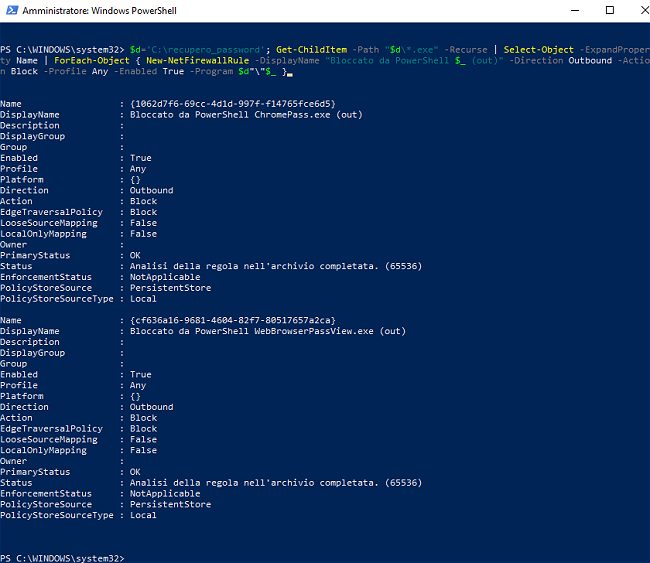
Explore the forensic perspective of the Microsoft Edge Chromium-based version and its features, such as msedge_proxy, edge cache location, and more | Group-IB Blog